Use our IT risk assessment template as a starting point to customize yours to fit your company.
IT Risk Assessment Template
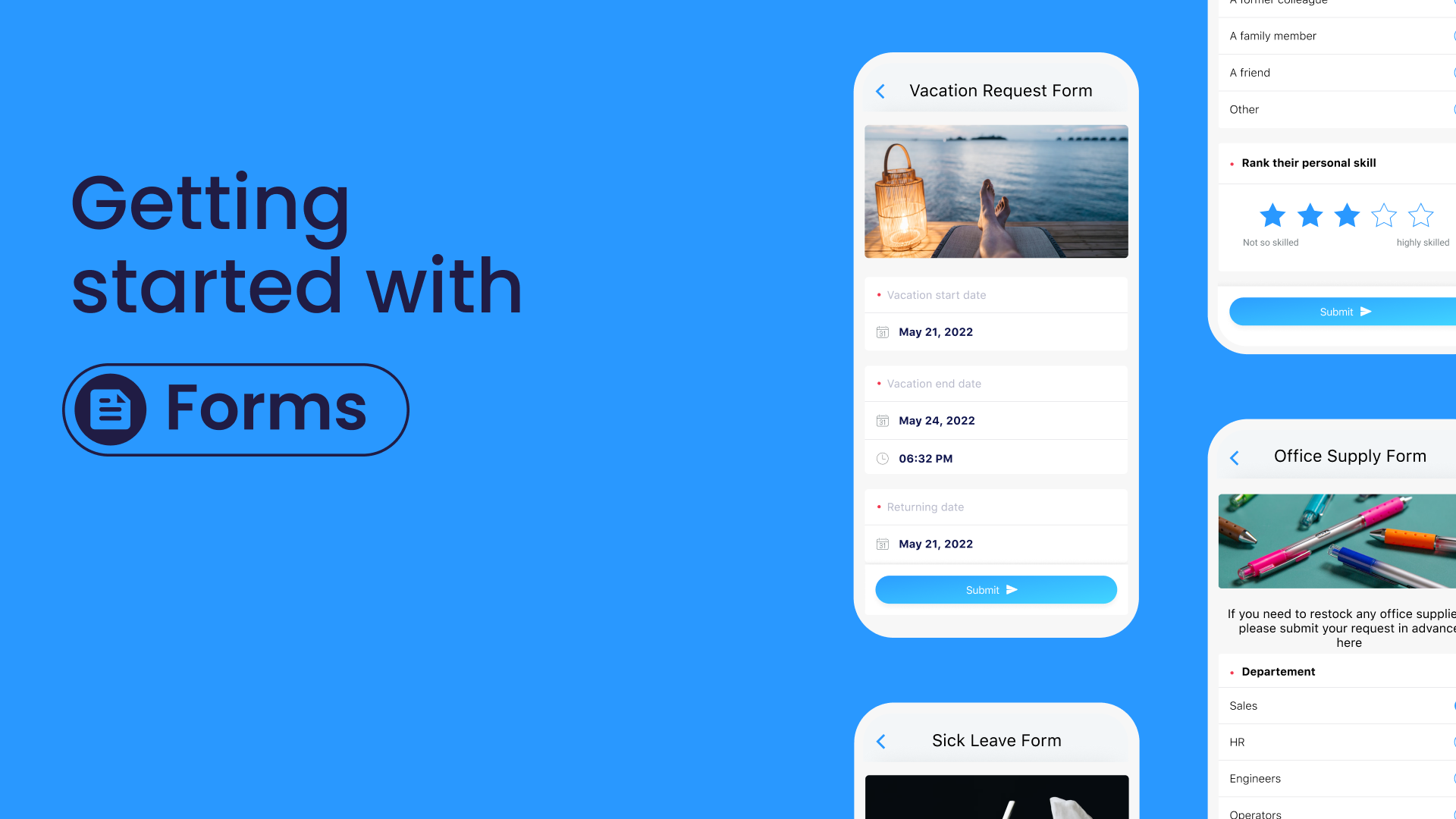
Make work flow with Connecteam’s digital forms & checklists
- Easily create digital forms and checklists for any task your team needs to complete on the job
- Boost accountability by having employees add a signature, image, or location stamp
- Save time by choosing from a variety of ready-made templates
- Instantly receive your team’s submissions and share reports within your organization
- Use AI to convert PDFs, Excel files, or images into digital forms in seconds—no manual work needed
IT Risk Assessment Template
An IT risk assessment is a systematic process for evaluating, identifying, and mitigating potential IT-related risks within an organization.
This template provides a structured framework for conducting an IT risk assessment to enhance cybersecurity, data protection, and overall IT resilience.
IT Risk Assessment Template
General Information:
[ ] Assessment Date: __________
[ ] Responsible Person/Team: __________
[ ] System/Process/Project: __________
Risk Identification:
Identify and list potential IT risks, including but not limited to:
[ ] Cybersecurity threats (e.g., malware, phishing, hacking).
[ ] Data breaches or leaks.
[ ] Hardware and software vulnerabilities.
[ ] Regulatory compliance risks.
[ ] Business continuity and disaster recovery concerns.
[ ] Third-party/vendor risks.
[ ] Personnel-related risks.
[ ] Emerging technology risks.
[ ] Rate each risk’s likelihood and potential impact (low, medium, high).
Risk Assessment:
Evaluate the identified risks:
[ ] Likelihood of occurrence.
[ ] Potential impact on IT systems, data, and the organization.
[ ] Current controls and safeguards in place.
[ ] Calculate the overall risk score for each identified risk.
[ ] Prioritize risks based on their risk scores.
Risk Mitigation and Control:
[ ] Develop mitigation strategies and controls for high and medium-risk items.
[ ] Specify responsible individuals or teams.
[ ] Set deadlines for implementation.
[ ] Identify required resources and budget.
[ ] Document the rationale for each mitigation strategy.
[ ] Monitor the progress of mitigation efforts.
[ ] Test and validate the effectiveness of controls.
Incident Response Planning:
[ ] Develop an incident response plan to address potential IT security incidents.
[ ] Define roles and responsibilities during incident response.
[ ] Establish communication protocols.
[ ] Conduct drills and exercises to ensure preparedness.
Documentation and Reporting:
[ ] Maintain comprehensive records of the risk assessment process.
[ ] Document risk assessment results, including identified risks, risk scores, and mitigation strategies.
[ ] Prepare a formal risk assessment report.
Review and Updates:
[ ] Schedule periodic reviews of the risk assessment.
[ ] Update the assessment to reflect changes in the IT landscape, technology, or business operations.
[ ] Ensure ongoing risk management and mitigation.
Signatures:
[ ] Responsible Person/Team: __________ Date: __________
An IT risk assessment is a crucial component of effective IT governance and cybersecurity.
By systematically identifying and addressing potential risks, organizations can enhance their IT resilience and protect sensitive data.
Regular reviews and updates to the risk assessment ensure that it remains aligned with evolving IT threats and organizational needs.
Choose Connecteam, the #1 Choice for IT Companies
Connecteam is the ultimate tool that can significantly enhance your IT company’s performance, streamlining your tasks and boosting productivity.
With our user-friendly mobile app, you can easily create and access checklists, ensuring every risk assessment is carried out to full satisfaction.
Keep track of all of your technicians and equipment right from within the app, and manage incident reports complete with photos and notes.
Plus, our smart scheduling and task management capabilities help you optimize work plans, ensuring perfectly staffed shifts and well-executed jobs.
Experience a game-changing solution tailored to your company’s needs!
Get started with Connecteam for free today and enjoy seamless checklists, instant reporting, and efficient collaboration with your team.
Watch the video below to see it in action:
Ready to boost your efficiency with our pre-made templates?